COPYRIGHTS & WRONGS
by John Henshall
©opyright.
A word which strikes fear in the mind of any
would-be transgressor. Oh yeah?
©opyright.
A word which raises the blood pressure of any
photographer who has had his images ripped-off. And quite rightly
so.
©opyright.
A law which none of us would ever violate. Not
never. Not no how.
Really? The Federation Against Copyright Theft (FACT) claims that
more than 21,000,000 pirate videos exist in UK homes and that this
jeopardises 47,000 jobs in the UK film industry.
Three years ago I made the mistake of saying, on a panel at 'Focus
On Imaging' 1994, that the 1988 Copyright Designs and Patents Act
would be about as much use, in this age of the Information
Superhighway, as the law which requires the drivers of motor vehicles
in Britain to have a man walking in front waving a red flag would be
in Motorway Britain.
'Mistake'? I meant what I said but forgot that we do have a
tradition of 'shooting the messenger' in this country.
Some folk took my remarks to be incitement to break the law. No
way. Just a warning that the policing of infringements is well nigh
impossible. Be realistic - how much time do you think the police have
to follow up every crime today? And how high would an infringement of
copyright figure in their league table of murders, muggings and
robberies? So you would probably have to do your own policing.
"Evenin' all. May I have a look at all the pictures you have at these
premises? Hello, hello, hello, what have we here then?" But isn't it
an offence to impersonate a police officer?
 Soon
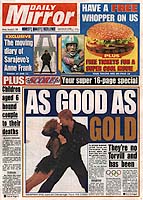
after I expressed my controversial opinion, I heard that the leader
of one of the photographic associations was so incensed that he was
checking my rights to all the images I had used in print. Such
processes were once called 'Witch Hunts'. A scan of the front page of
the 'Daily Mirror' was identified as my possible downfall. I had
scanned the paper to show the use of digital photography from the
Lillehammer Winter Olympics and had taken care to obtain the
permission of the photographer (Phil O'Brien of Empics) - but what
about the other elements of the front page? My heart sank, so I
telephoned Mike Ives, the Mirror's Night Picture Editor, to throw
myself on his mercy. "Did you reproduce the whole of page one?" he
asked. "I'm afraid so," I admitted. "That's fine - no problem - it's
what we call a 'rag out'."
Soon
after I expressed my controversial opinion, I heard that the leader
of one of the photographic associations was so incensed that he was
checking my rights to all the images I had used in print. Such
processes were once called 'Witch Hunts'. A scan of the front page of
the 'Daily Mirror' was identified as my possible downfall. I had
scanned the paper to show the use of digital photography from the
Lillehammer Winter Olympics and had taken care to obtain the
permission of the photographer (Phil O'Brien of Empics) - but what
about the other elements of the front page? My heart sank, so I
telephoned Mike Ives, the Mirror's Night Picture Editor, to throw
myself on his mercy. "Did you reproduce the whole of page one?" he
asked. "I'm afraid so," I admitted. "That's fine - no problem - it's
what we call a 'rag out'."
How, then, do we look after our copyrights? Do you want to spend
time in a draughty court room corridor, perhaps wasting good earning
time, trying to get Grandpa Smith convicted for making colour laser
copies of his grand children's portraits to 'sell' on to his
children? Be realistic, only the lawyers would profit and no jury
would be likely to convict Grandpa Smith - whether it's the law or
not.
Although ignorance is normally no defence in the eyes of the law,
incredibly, it can be in the case of copyright. And a jury might well
feel that, if he'd paid for the portraits, Mr Smith was entitled to
copy them as he wished. Take a straw poll among ordinary people you
meet. I did. Nearly all I asked felt that making copies would be
perfectly legal. And all these 'ordinary people' are the kind you
would find sitting on a jury. It's a bad law if the world at large
don't know about it or understand it.
Suppose now that Grandpa Smith was a photographer, or even a
lawyer. That might put a completely different complexion on matters.
In natural justice, knowing that something is wrong is much worse
than mere ignorance.
Like many of you, I have had my copyright infringed on many
occasions.
 One
particular image, of a Horse Guard in Whitehall, has been very
popular. Undeleted - with my permission - from a digital camera
returned to the manufacturer after review, the image soon found its
way out - without my permission - as a digital file sent to
distributors, and printed out and framed for the wall of the office.
It even appeared as an illustration to someone else's review in the
UK edition of MacWorld - though I know that the editor acted in good
faith, believing that it was copyright cleared. The first mistake I
had made was in not irretrievably re-formatting the camera before
return, rather than just nominally deleting the images. I then
allowed a respectable and trustworthy employee of the company to
undelete the image for his own interest and use. Then someone else
saw the image on his computer and took it to be alright to use for
other purposes. Another mistake I made was in allowing the image file
to be included on a CD accompanying a book, without first burning-in
a big copyright notice.
One
particular image, of a Horse Guard in Whitehall, has been very
popular. Undeleted - with my permission - from a digital camera
returned to the manufacturer after review, the image soon found its
way out - without my permission - as a digital file sent to
distributors, and printed out and framed for the wall of the office.
It even appeared as an illustration to someone else's review in the
UK edition of MacWorld - though I know that the editor acted in good
faith, believing that it was copyright cleared. The first mistake I
had made was in not irretrievably re-formatting the camera before
return, rather than just nominally deleting the images. I then
allowed a respectable and trustworthy employee of the company to
undelete the image for his own interest and use. Then someone else
saw the image on his computer and took it to be alright to use for
other purposes. Another mistake I made was in allowing the image file
to be included on a CD accompanying a book, without first burning-in
a big copyright notice.
Of course I could have taken action. But what you have to take
into account is that you will, almost certainly, lose the client. So
I decided to grin and bear it, trying to be flattered that so many
people thought the image worthwhile. The indignity followed soon
afterwards, when the company's PR agents phoned to ask if they could
use the image for another client. I quoted a very reasonable
£100, only to be told that they expected only to give me a
name-check. Explaining that my family couldn't get nourishment from
credits made no difference, so the conversation ended with a very
brief goodbye, the second and last word of which was "off".
That same image is now on my website. But is it safe here? With
experiences such as this, it would be easy to become paranoid -
indeed many photographers and photo libraries are too scared to put
their images on the web in case they are pirated. The fact is that a
pirate could get better results by re-scanning the picture from the
pages of a magazine than by using a low-resolution, highly compressed
digital file from the Internet.

An enlarged section
of the original camera file

Section of the
printed image as reproduced in 'The Photographer' August 1994,
re-scanned from the printed page using Agfa DuoScan desktop flatbed
scanner.


Same section from
the version here on the website. Note the lower resolution - the
quality of an image scanned from the printed page is much higher. If
the whole of the web-resolution image was reproduced on a printed
page at 300 ppi, the resolution would only provide a sharp image 1 x
1.5 inches.
Recently I have had my copyright infringed both by another
photographer and by a lawyer. Both should have known better,
especially the legal man, who once was a frequent writer on the
subject. No one is perfect, but we should always try to practice what
we preach.
These recent infringements of my copyrights were of images I had
placed on the Internet. If the pirate wants only to re-use your image
on his own website, copying it from the Internet is very easy. It
even saves the job of scanning and the little-understood techniques
(especially among inexperienced web designers) of effective image
compression to save bandwidth and reduce download times. It's not
just text and photographs which are the problem, background images
and scans of logos are copyright too.
 My
image of a grey background may not look much but it took about a
fortnight to get right. First, I read Ansel Adams' autobiography,
where he expressed his opinion about the best background on which to
display prints. Taking his views into account, I made up a
distinctive textured background image and spent a lot of time
adjusting the levels to make it work well on computers with displays
ranging from 256 to over 16 million colours. Not only does this work
well with images but it gives the website a distinctive
look.
My
image of a grey background may not look much but it took about a
fortnight to get right. First, I read Ansel Adams' autobiography,
where he expressed his opinion about the best background on which to
display prints. Taking his views into account, I made up a
distinctive textured background image and spent a lot of time
adjusting the levels to make it work well on computers with displays
ranging from 256 to over 16 million colours. Not only does this work
well with images but it gives the website a distinctive
look.
To make the BIPP website different, I used a warm version of the
same texture. When a copyright expert used this and my scan of the
BIPP logo without permission on his website well, it's wrong but
hardly time for court action. To err is human - in fact, it's
reassuring to find that he's only human, too.
The best way to learn to design web pages is to look at what
others have done. Surf the web until you find someone else's page you
like, then select View>Document Source and you are immediately
into the HTML code which makes the page work. In the HTML are details
of the jpg and gif format files which the web page uses. It really is
that easy, so it's very tempting to 'borrow' ideas and elements to
start your own website. The whole ethos of the web is free and easy,
so it's easy to forget that everything here is copyright.
Way back in 1994, when the Internet was still little used by the
masses, that same leader of another photographic association ventured
to suggest that even the displaying of someone else's images on your
computer was a copyright infringement. So where would this leave us
with viewing web pages? It would be taking matters too far to suggest
that this constitutes a copyright infringement. But suppose you like
the pages you see and decide to save code to your hard drive for
analysis? Or you make hard-copy prints? And what about the fact that
web browsers actually copy images to a cache, to save downloading
them next time the page is accessed. This caching involves
transferring the images from someone's web server to your hard drive.
You have copied the images - probably without realising it. But, when
you log off, it would be quite possible to find the cached file of my
Guard and open it in Adobe Photoshop. Now we really are in a grey
area as far as copyright is concerned. Hopefully, what your browser
has done for you can be defended as 'fair use'.
 So
where do we seek advice? There is an essential book about the law as
it applies to photography. Adrian Berkeley's 'The Focal Guide to
Photography and the Law' (ISBN 0 240 51352 5, published by
Butterworth-Heinemann Ltd, £12.95) is a mine of important
information. Unfortunately, being a book published 'way back' in
1993, in Internet terms it is not very comprehensive and not kept up
to date.
So
where do we seek advice? There is an essential book about the law as
it applies to photography. Adrian Berkeley's 'The Focal Guide to
Photography and the Law' (ISBN 0 240 51352 5, published by
Butterworth-Heinemann Ltd, £12.95) is a mine of important
information. Unfortunately, being a book published 'way back' in
1993, in Internet terms it is not very comprehensive and not kept up
to date.
This highlights some of the major advantages of the Internet over
conventional publishing. It is easy to update an Internet page with
the latest amendments to a document. With a printed book, you have to
wait until the next edition comes out. Add to this the time taken to
print and distribute a book and the chances are it will be out of
date before it reaches the bookshops. Another advantage of the
Internet is that authors do not need to defer to the press barons.
The Internet has no expensive presses to control. The Internet is
democratic; there is no power to wield. That is precisely why the big
publishers are so worried about their futures. Of course, it is also
more difficult for authors to get payment for their work on the
Internet - but then it's difficult enough to earn more than a
pittance for non-fiction.
If you are not already on the Internet I recommend that you
subscribe to a dial-up service without delay. Imagine having the
world's biggest reference library, constantly updated by millions of
small publishers, just a mouse-click away. The importance of this
resource is truly immense.
I used the Internet to search for items on copyright and came up
with The Copyright Website
which gives some well reasoned advice. But it's all about what's
right and wrong - the [American] law - and we know that folk
break the law, either unintentionally or deliberately. So what's the
answer? What can we do about the problem?
One thing is clear: prevention would be better than cure. Stephen
Johnson, a digital landscape photographer from Pacifica, California,
maintains control by keeping his digital files to himself. That will
do for those of us who have to deliver final prints but it will not
cover those of us who have to send out digital files, for pre-press,
for example. How do you restrict the use of your images if you must
send images in digital form, or post them on the web?
With the increasing use of writable CD-ROM and the Internet as
ways for photographers and photo libraries to display and deliver
their images to potential clients, the need for an efficient
protection scheme has become urgent.
 'Code
Cryptor' is an encryption program for protecting data on CD, computer
disks and web sites. It uses the US Government Data Encryption
Standard (DES) which has proven to be unbreakable, so far. It has a
drag-and-drop interface and can generate Smart PIN (Personal
Information Numbers) like those used to draw money from the banks'
ATMs.
'Code
Cryptor' is an encryption program for protecting data on CD, computer
disks and web sites. It uses the US Government Data Encryption
Standard (DES) which has proven to be unbreakable, so far. It has a
drag-and-drop interface and can generate Smart PIN (Personal
Information Numbers) like those used to draw money from the banks'
ATMs.
It is very easy to use. To encrypt a file, simply drag it onto the
'nCryptor' icon. The program creates a new folder entitled
'Encrypted', into which is placed the encrypted file and a linked
Token - the private key that will be used to unlock the file. You can
now send the encrypted file via the Internet or electronic mail - or
'burn' it onto CD-ROM or any other form of disk. The file cannot be
viewed or used by anyone - other than the person to whom you have
given the Token or smart PIN.
To maintain maximum security, the Token must be kept completely
separate from the encrypted image file, and should be passed on to
the client by other means, such as fax, or over the phone.
Once a file is encrypted, there is no way to trace the type of
program used to create it. nCryptor scrambles the document to the
point that it simply appears as a string of data. The Code Cryptor
suite of software is Cross platform - Mac, PC and Unix - and will
encrypt files created on all existing software. To decrypt the file,
the recipient first drags the token onto the dCryptor icon, then
drags the encrypted document icon onto the dCryptor icon. The
decrypted file is placed into a newly created folder entitled
'Decrypted'. The user double-clicks the folder, double-clicks the
document, and it opens. It is not even necessary for the client to
own dCryptor, which is supplied free of charge.
Smart PINS allow the encryption of a CD-ROM containing any number
of stock shots with a Token. You can then assign each individual
customer a Smart PIN to unlock the images specified in the contract.
The buyer can unlock the CD using the Smart PIN and access
high-resolution versions of the images. Because the Smart PINs can be
grouped together, the user doesn't have to enter a password for each
image on the CD-ROM
Vital Source Technologies of San Antonio, Texas, are using Code
Cryptor to protect medical information on CDs. The industrial version
of the software contains a product called Code Plus, which has
several additional features which will be useful for companies trying
to protect their images. Code Plus can write a Smart PIN into the
file itself and the Smart PIN can be traced back to the original
customer. By maintaining a database of the Smart PINs, you can track
who bought which images and when. This information can also be used
to generate invoices. These file copies must be kept in a safe
location in the event that a Token or Smart PIN is lost, for the
Token is the only record that contains the information for the
cryptographic key. Without it, you are out of luck. If you lose the
Token, you lose the data.
The US Data Encryption Standard (DES) is reviewed every five
years. And, because it is based on the cryptographic key - a randomly
generated alphanumeric password - it has proved unbreakable for
almost twenty years. It is thus one of the most secure styles of
encryption available.
At the 1997 PMA convention in New Orleans in February 1996, Code
Cryptor was selected, as one of the most innovative and promising
technologies.
Free demonstration software is available from New
Mexico Software Europe, or telephone +44 (0)1992 589579.
This article first appeared as "John Henshall's Chip
Shop" in "The Photographer" magazine, April 1997.
IMPORTANT NOTICE
This document is Copyright © 1997 John Henshall. All rights
reserved.
This material may only be downloaded for personal non-commercial use.
Please safeguard the future of online publishing by respecting this
copyright and the rights of all other authors of material on the
Internet.

 Soon
after I expressed my controversial opinion, I heard that the leader
of one of the photographic associations was so incensed that he was
checking my rights to all the images I had used in print. Such
processes were once called 'Witch Hunts'. A scan of the front page of
the 'Daily Mirror' was identified as my possible downfall. I had
scanned the paper to show the use of digital photography from the
Lillehammer Winter Olympics and had taken care to obtain the
permission of the photographer (Phil O'Brien of Empics) - but what
about the other elements of the front page? My heart sank, so I
telephoned Mike Ives, the Mirror's Night Picture Editor, to throw
myself on his mercy. "Did you reproduce the whole of page one?" he
asked. "I'm afraid so," I admitted. "That's fine - no problem - it's
what we call a 'rag out'."
Soon
after I expressed my controversial opinion, I heard that the leader
of one of the photographic associations was so incensed that he was
checking my rights to all the images I had used in print. Such
processes were once called 'Witch Hunts'. A scan of the front page of
the 'Daily Mirror' was identified as my possible downfall. I had
scanned the paper to show the use of digital photography from the
Lillehammer Winter Olympics and had taken care to obtain the
permission of the photographer (Phil O'Brien of Empics) - but what
about the other elements of the front page? My heart sank, so I
telephoned Mike Ives, the Mirror's Night Picture Editor, to throw
myself on his mercy. "Did you reproduce the whole of page one?" he
asked. "I'm afraid so," I admitted. "That's fine - no problem - it's
what we call a 'rag out'." One
particular image, of a Horse Guard in Whitehall, has been very
popular. Undeleted - with my permission - from a digital camera
returned to the manufacturer after review, the image soon found its
way out - without my permission - as a digital file sent to
distributors, and printed out and framed for the wall of the office.
It even appeared as an illustration to someone else's review in the
UK edition of MacWorld - though I know that the editor acted in good
faith, believing that it was copyright cleared. The first mistake I
had made was in not irretrievably re-formatting the camera before
return, rather than just nominally deleting the images. I then
allowed a respectable and trustworthy employee of the company to
undelete the image for his own interest and use. Then someone else
saw the image on his computer and took it to be alright to use for
other purposes. Another mistake I made was in allowing the image file
to be included on a CD accompanying a book, without first burning-in
a big copyright notice.
One
particular image, of a Horse Guard in Whitehall, has been very
popular. Undeleted - with my permission - from a digital camera
returned to the manufacturer after review, the image soon found its
way out - without my permission - as a digital file sent to
distributors, and printed out and framed for the wall of the office.
It even appeared as an illustration to someone else's review in the
UK edition of MacWorld - though I know that the editor acted in good
faith, believing that it was copyright cleared. The first mistake I
had made was in not irretrievably re-formatting the camera before
return, rather than just nominally deleting the images. I then
allowed a respectable and trustworthy employee of the company to
undelete the image for his own interest and use. Then someone else
saw the image on his computer and took it to be alright to use for
other purposes. Another mistake I made was in allowing the image file
to be included on a CD accompanying a book, without first burning-in
a big copyright notice.



 My
image of a grey background may not look much but it took about a
fortnight to get right. First, I read Ansel Adams' autobiography,
where he expressed his opinion about the best background on which to
display prints. Taking his views into account, I made up a
distinctive textured background image and spent a lot of time
adjusting the levels to make it work well on computers with displays
ranging from 256 to over 16 million colours. Not only does this work
well with images but it gives the website a distinctive
look.
My
image of a grey background may not look much but it took about a
fortnight to get right. First, I read Ansel Adams' autobiography,
where he expressed his opinion about the best background on which to
display prints. Taking his views into account, I made up a
distinctive textured background image and spent a lot of time
adjusting the levels to make it work well on computers with displays
ranging from 256 to over 16 million colours. Not only does this work
well with images but it gives the website a distinctive
look.
 So
where do we seek advice? There is an essential book about the law as
it applies to photography. Adrian Berkeley's 'The Focal Guide to
Photography and the Law' (ISBN 0 240 51352 5, published by
Butterworth-Heinemann Ltd, £12.95) is a mine of important
information. Unfortunately, being a book published 'way back' in
1993, in Internet terms it is not very comprehensive and not kept up
to date.
So
where do we seek advice? There is an essential book about the law as
it applies to photography. Adrian Berkeley's 'The Focal Guide to
Photography and the Law' (ISBN 0 240 51352 5, published by
Butterworth-Heinemann Ltd, £12.95) is a mine of important
information. Unfortunately, being a book published 'way back' in
1993, in Internet terms it is not very comprehensive and not kept up
to date. 'Code
Cryptor' is an encryption program for protecting data on CD, computer
disks and web sites. It uses the US Government Data Encryption
Standard (DES) which has proven to be unbreakable, so far. It has a
drag-and-drop interface and can generate Smart PIN (Personal
Information Numbers) like those used to draw money from the banks'
ATMs.
'Code
Cryptor' is an encryption program for protecting data on CD, computer
disks and web sites. It uses the US Government Data Encryption
Standard (DES) which has proven to be unbreakable, so far. It has a
drag-and-drop interface and can generate Smart PIN (Personal
Information Numbers) like those used to draw money from the banks'
ATMs.